Attackers behind information-stealing malware known as typhon reborn It has resurfaced in an updated version (V2) with improved capabilities to evade detection and resist analysis.
The new version sells for $59/month, $360/year, or $540 for a lifetime subscription on the criminal underworld.
“A stealer can collect and steal sensitive information and use the Telegram API to send the stolen data to the attacker,” said Cisco Talos researcher Edmund Brumaghin. Said in Tuesday’s report.
Typhon is first documented Created by Cyble in August 2022, it has a myriad of features such as hijacking clipboard content, capturing screenshots, logging keystrokes, crypto wallets, messaging, stealing data from FTP, VPN, browsers, gaming apps, etc. is explained in detail.
Typhon can also deliver the XMRig cryptocurrency miner based on another stealer malware called Prynt Stealer. In November 2022, Palo Alto Networks Unit 42 unearthed an updated version called Typhon Reborn.
“Anti-analysis technology has been enhanced in this new version and has been modified to improve stealer and file grabber functionality,” Unit 42 said, adding that existing features such as keylogging and cryptocurrency mining have been removed. and clearly trying to reduce the chances of detection. .
According to Cisco Talos, the latest V2 variant was sold by a developer on the Russian dark web forum XSS on January 31, 2023.
“Typhon Reborn Stealer is a heavily refactored and improved version of the old and unstable Typhon Stealer,” said the malware author, touting its cheap price and absence of backdoors.
Like other malware, V2 comes with options to avoid infecting systems located in Commonwealth of Independent States (CIS) countries. However, Ukraine and Georgia are excluded from the list.
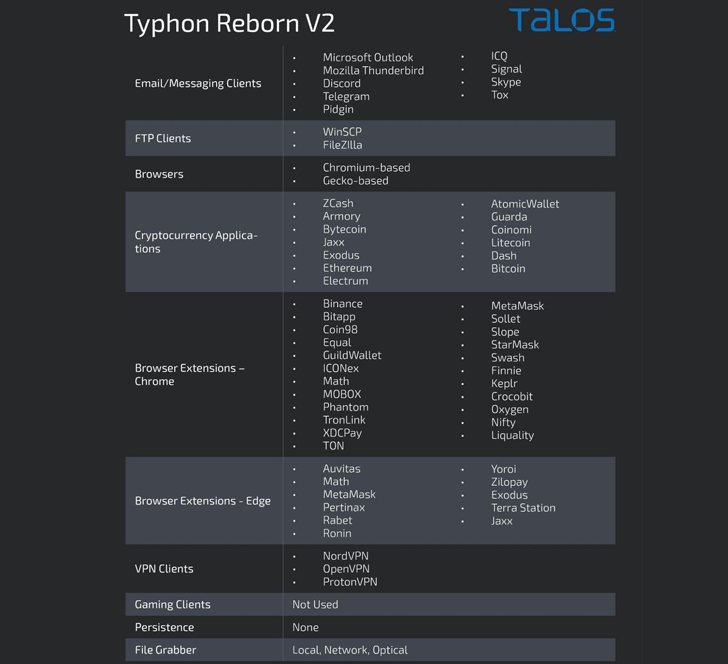
In addition to incorporating more anti-analysis and anti-virtualization checks, Typhon Reborn V2 removes its persistence functionality, opting instead to terminate itself after data exfiltration.
The malware eventually uses the Telegram API to send the collected data in a compressed archive over HTTPS, demonstrating continued abuse of the messaging platform.
“Once the data is sent to the attacker, the archive is removed from the infected system,” said Brumaghin. “Then the malware [a self-delete function] Finish execution. ”
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
The findings came when Cyble revealed a new Python-based stealer malware named Creal. This malware targets cryptocurrency users through phishing sites that mimic legitimate cryptocurrency mining services like Kryptex.
This malware is similar to Typhon Reborn in its ability to siphon data from instant messaging, games, and crypto wallet apps, as well as cookies and passwords from Chromium-based web browsers.
However, the malware’s source code is available on GitHub, so other threat actors can modify it to suit their needs and make it a powerful threat.
“Creal Stealer can exfiltrate data using Discord webhooks and multiple file hosting and sharing platforms such as Anonfiles and Gofile,” Cyble said. Said In a report released last week.
“The trend among cybercriminals to use open source code for malware is increasing because it allows them to create sophisticated and customized attacks at minimal cost.”


