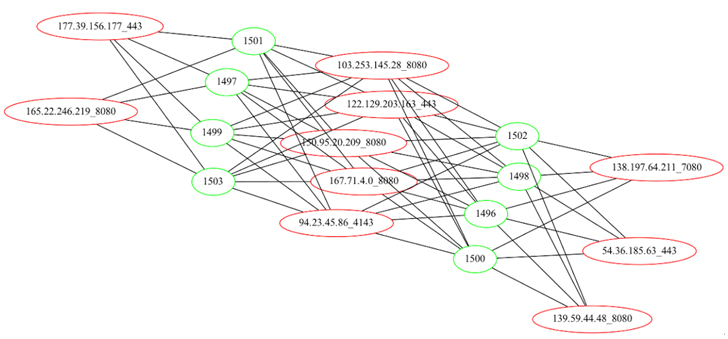
The infamous Emotet malware has returned with renewed vigor as part of a mass malspam campaign designed to drop payloads such as IcedID and Bumblebee.
Enterprise security company Proofpoint, sending “hundreds of thousands of emails a day” since early November 2022 Said Last week, it added, “New activity suggests Emotet is back to full functionality serving as a delivery network for major malware families.”
The main target countries are USA, UK, Japan, Germany, Italy, France, Spain, Mexico and Brazil.
Emotet-related activity was last observed in July 2022, but sporadic infections have been reported since then. In mid-October, ESET revealed that Emotet may be gearing up for a new wave of attacks, pointing to updates to the “systeminfo” module.
The malware, believed to be attributed to the threat actor known as Mummy Spider (aka Gold Crestwood or TA542), made a resurgence of sorts late last year after a coordinated law enforcement effort dismantled its infrastructure in January 2021. achieved.
Europol calls Emotet “the most dangerous malware in the world”. This is due to its ability to act as a “main door opener for computer systems” for deploying next-stage binaries that facilitate data theft and ransomware. It started as a banking Trojan in 2014 and has evolved into a botnet.
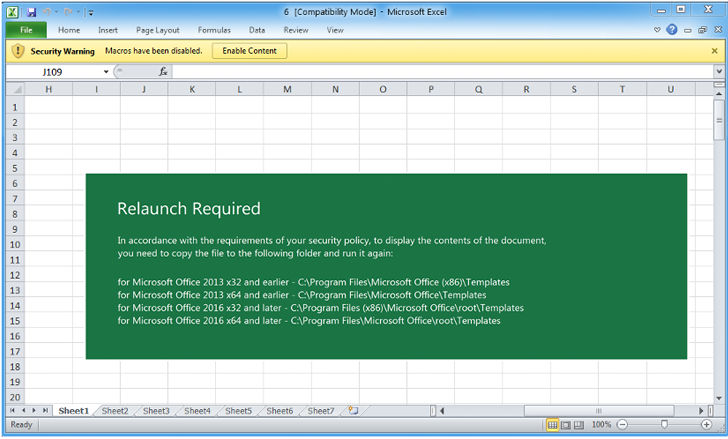
Infection chains involving malware are known to use common lures and email thread hijacking techniques to lure recipients into opening macro-enabled Excel attachments.
“Following Microsoft’s recent announcement to disable macros by default in Office documents downloaded from the Internet, many malware families have begun to move away from Office macros to other delivery mechanisms such as ISO and LNK files.” says Cisco Talos. Said Early this month.
“It is therefore interesting to note that this new Emotet campaign uses the old method of distributing malicious Microsoft Office documents (maldocs) via email-based phishing.
Another method is to encourage potential victims to copy the file to a Microsoft Office Templates location (a trusted location) and launch the lure document from there. You don’t need to explicitly enable the macro to activate the kill her chain.
of Resume activities It also modifies the Emotet loader component, adds new commands, and updates the packer to resist reverse engineering.
One of the subsequent payloads distributed via Emotet is an entirely new variant of the IcedID loader that accepts commands to read file contents and send them to remote servers, and other payloads that allow it to extract web browser data. Execute backdoor instructions.
Researchers note that the use of IcedID is of concern as it is likely a predecessor of ransomware. Another malware dropped via Emotet bumblebeeaccording to Palo Alto Networks Unit 42.
“Overall, these changes to the client show that developers are trying to deter researchers and reduce the number of fake or captive bots that exist within the botnet,” said the researchers. said Pim Trouebach and Axel F of
“Emotet has not demonstrated full functionality and consistent subsequent payload delivery (not Cobalt Strike) since 2021, when distribution of The Trick and Qbot was observed.”


