Iranian threat actor known as domestic kitten has been attributed to a new mobile campaign disguised as a translation app to distribute an updated variant of Android malware known as FurBall.
“Since June 2021, it has been distributed as a translation app mimicking Iranian websites offering translated articles, magazines and books,” said ESET researcher Lukas Stefanko. . Said In a report shared with The Hacker News.
The update is designed to avoid detection by security solutions while retaining the same monitoring capabilities as the previous version, the Slovak cybersecurity firm added.
Domestic Kitten (also known as APT-C-50) is an Iranian threat activity cluster previously observed targeting individuals of interest in order to collect sensitive information from compromised mobile devices. Known to be active since at least 2016.
A tactical analysis conducted by Trend Micro in 2019 revealed potential ties to another group called Domestic Kitten. bouncing golfa cyber espionage campaign targeting Middle Eastern countries.
According to Check Point, APT-C-50 is primarily targeted at “Iranian forces that could pose a threat to the stability of the Iranian regime, including internal dissidents, opposition forces, ISIS defenders, and Kurdish minorities inside Iran.” “National” is selected.
Campaigns carried out by this group have traditionally relied on luring potential victims into installing malicious applications through various attack vectors such as Iranian blog sites, Telegram channels, and SMS messages. .
Regardless of the method employed, the app acts as a conduit to deliver pieces of malware codenamed by an Israeli cybersecurity firm named Furball. Furball is a customized version of KidLogger with the ability to collect and steal personal data from devices.
The latest campaign uncovered by ESET involves an app pretending to be a translation service. Previous covers used to hide malicious behavior spanned various categories, including security, news, games, and wallpaper apps.
App (“sarayemaghale.apk“) is delivered via fake websites that mimic downloads.[.]A legitimate site that provides articles and books translated from English to Persian.
It’s worth noting that the latest version maintains the spyware’s core functionality, while the artifact only requests one permission to access contacts, SMS messages, device location, call logs, and clipboard data. is restricting access to
“The reason may be to stay under the radar. On the other hand, we believe it may also represent a precursor to spear phishing attacks conducted via text messages. ,” pointed out Stefanko.
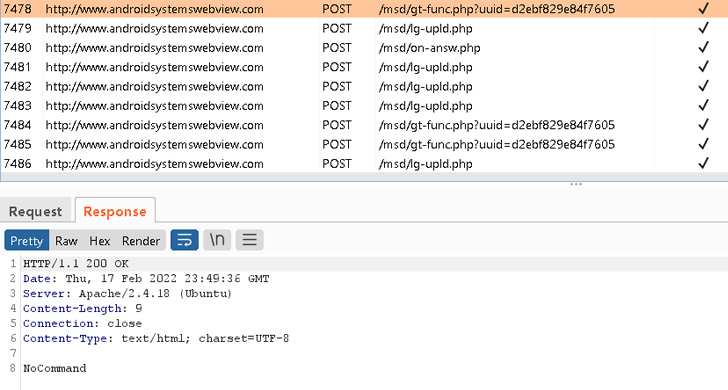
Despite this handicap, in its current form, Furball malware takes commands from remote servers to retrieve contacts, files from external storage, lists of installed apps, basic system metadata, and synchronized files. can collect user accounts.
Despite the reduction in active app functionality, the sample further stands out by implementing a rudimentary code obfuscation scheme that is seen as an attempt to overcome security barriers.
“Domestic kitten campaigns are still active, using copycat websites to target Iranian citizens,” Stefanko said. changed slightly to a different variant.”




