The notorious Emotet botnet has been linked to a wave of new malware campaigns that utilize password-protected archive files to drop CoinMiner and Quasar RAT onto compromised systems.
and attack chain An invoice-themed ZIP file lure detected by Trustwave SpiderLabs researchers was found to contain a nested self-extracting (SFX) archive.
While such phishing attacks traditionally require the target to be persuaded to open the attachment, cybersecurity firms have reported that the campaign utilizes a batch file to automatically provide the password to unlock the payload. By providing it, it says it bypasses this hurdle.
The first SFX archive file also uses a PDF or Excel icon to appear legitimate, but is actually a second password-protected SFX RAR file, the aforementioned batch script to launch the archive, and a decoy. PDF or image.
“Running the batch file installs malware hidden inside a password-protected RARsfx. [self-extracting RAR archive]said researchers Bernard Bautista and Diana Lopera in an article on Thursday.
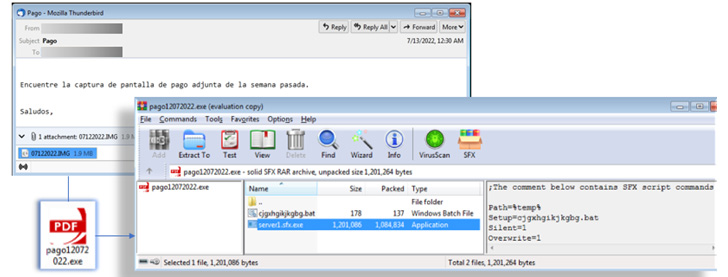
The batch script accomplishes this by specifying the password for the archive and the folder where the payload should be extracted, as well as launching a command to display the lure document to hide the malicious activity.
Finally, the infection culminates in the execution of CoinMiner. CoinMiner is a cryptocurrency miner that can also steal credentials. Quasar RATopen source .NET based remote access trojandepending on the payload packed in the archive.
One-click attack techniques are also notable for effectively bypassing password barriers, enabling malicious actors to perform a wide range of actions including cryptojacking, data exfiltration, and ransomware.
Trustwave has seen an increase in threats packaged in password-protected ZIP files, saying about 96% of them are distributed by the Emotet botnet.
“Self-extracting archives have been around for a long time, facilitating file distribution between end users,” said the researchers. “However, it poses a security risk because you cannot easily see the contents of the file and can run commands and executables in silent mode.”




