A new botnet called dark frost It has been observed launching distributed denial of service (DDoS) attacks against the gaming industry.
“The Dark Frost botnet, modeled after Gafgyt, QBot, Mirai, and other malware strains, has scaled to encompass hundreds of compromised devices,” said Allen West, a security researcher at Akamai. . Said In a new technical analysis shared with The Hacker News.
Targets include game companies, game server hosting
Providers, online streamers, and even members of other gaming communities with whom the threat actor has interacted directly.
As of February 2023, the botnet consists of 414 machines running various instruction set architectures such as ARMv4, x86, MIPSEL, MIPS and ARM7.
Botnets typically consist of vast networks of compromised devices around the world. Operators can use enslaved hosts to mine cryptocurrency, steal sensitive data, or leverage the collective internet bandwidth from these bots to flood their targets with junk traffic and other tends to bring down his website and Internet servers.
Dark Frost represents the latest version of a botnet that appears to have been stitched together by stealing source code from various botnet malware strains such as Mirai, Gafgyt, and QBot.
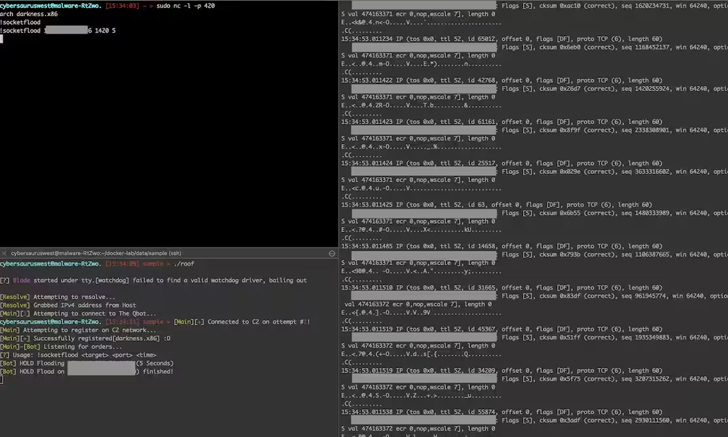
After flagging the botnet on February 28, 2023, Akamai reverse-engineered it and estimated the attack potential to be approximately 629.28 Gbps. UDP flood attack. This threat actor is believed to have been active since at least May 2022.
“What’s interesting about this particular case is that the actors behind these attacks have published live recordings of the attacks for everyone to see,” said the web infrastructure company.
“The attackers have been observed boasting about their achievements on social media, using botnets to facilitate minor online disputes, and leaving digital signatures on binary files. ”
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
The adversary also established a Discord channel to facilitate the attack in exchange for money, demonstrating financial motives and plans to materialize as a DDoS rental service.
Dark Frost is a modern-day example of how easy it is for novice cybercriminals with rudimentary coding skills to take action with already available malware and wreak havoc on businesses. It is
“The reach of these threat actors is staggering despite the novelty of their techniques,” said West. “The Dark Frost botnet is not the most advanced or daunting adversary, yet it has managed to amass hundreds of infected devices to carry out its commands. increase.”


