Cybersecurity researchers have exposed an internal structure called a new wiper Azov ransomware It is designed to intentionally destroy data and “cause irreproachable damage” to compromised systems.
Distributed via another malware loader known as SmokeLoader, the malware explained As an “effective, fast and unfortunately unrecoverable data wiper” by Israeli cybersecurity firm Check Point.
The wiper routine is set to overwrite the file contents using alternating chunks of 666 bytes and random noise. intermittent encryption This is increasingly being leveraged by ransomware operators to evade detection and encrypt victims’ files more quickly.
“One of the differences between ransomware in general and Azov is that it modifies certain 64-bit executables to run their own code,” says threat researcher Jiří Vinopal. said Mr. “Modification of the executable is done using polymorphic code so that static signatures cannot possibly fail.”
Azov Ransomware also incorporates logic bombs (a set of conditions that must be met before activating malicious actions) that detonate the execution of erasing and backdoor functions at predetermined times.
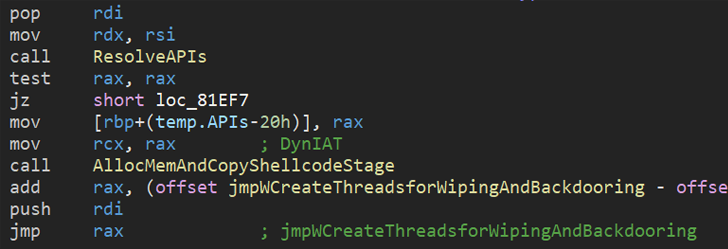
“The Azov sample was considered skidware when first encountered, […]Further investigation reveals manually crafted assemblies, highly sophisticated techniques for injecting payloads into executables to create backdoors, and typically for security textbooks or well-known brand name cybercriminal tools. You will find some anti-analysis tricks reserved for ,” Vinopal added.
This development comes amid a slew of devastating wiper attacks since the beginning of the year. This includes WhisperGate, HermeticWiper, AcidRain, IsaacWiper, CaddyWiper, Industroyer2, DoubleZero, RURansom, and CryWiper.
Last week, security firm ESET revealed another unknown wiper called Fantasy. This wiper was spread using a supply chain attack that targeted an Israeli software company and targeted customers in the diamond industry. This malware is associated with an actor called Agrius.



