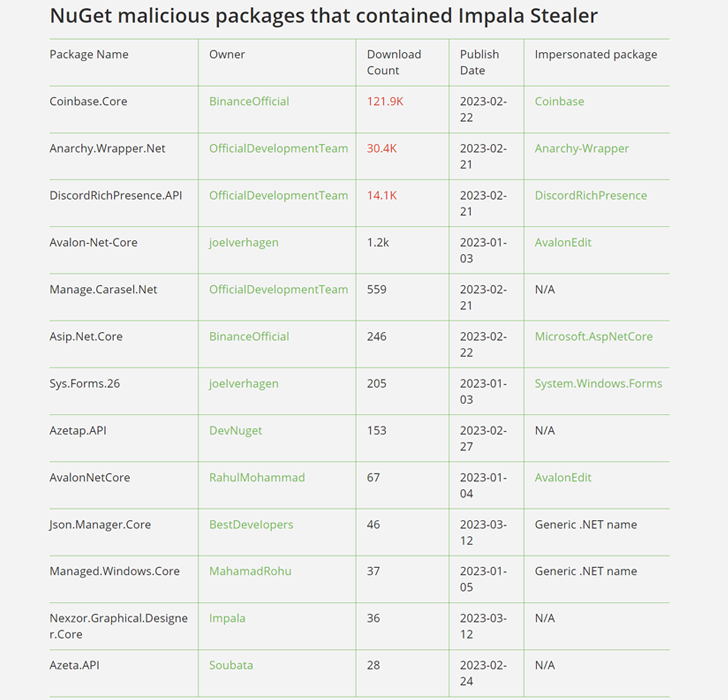
Cybersecurity researchers delved into the inner workings of a cryptocurrency stealer malware distributed via 13 malicious NuGet packages as part of a supply chain attack targeting .NET developers.
A sophisticated typosquatting campaign, detailed by JFrog late last month, impersonated a legitimate package and ran PowerShell code designed to retrieve subsequent binaries from hardcoded servers. .
of double attack Ultimately, a persistent .NET-based backdoor called Impala Stealer was deployed to allow unauthorized access to users’ cryptocurrency accounts.
“The payload used a very rare obfuscation technique called ‘.NET AoT compilation’, which made reverse-engineering the binaries more difficult, but still more efficient than using ‘off-the-shelf’ obfuscation tools. It’s also much more stealthy,” JFrog told The Hacker News. statement.
.Net AoT compilation is Optimization method This allows you to pre-compile your app to native code. Native AOT apps have faster startup times, a smaller memory footprint, and can run on machines that don’t have the .NET runtime installed.
The second stage payload comes with an auto-update mechanism that allows newer versions of the executable to be retrieved from remote locations. Additionally, persistence is achieved by injecting JavaScript code into Discord or Microsoft Visual Studio Code apps, thereby activating the launch of the stealer binary.
The binary then searches for installations of the Exodus Wallet desktop application and injects JavaScript code into various HTML files to collect and extract sensitive data into hardcoded Discord webhooks.
The snippet of JavaScript is taken from an online paste website that has since been removed. That said, we suspect this code was used to steal user credentials and access other information of interest.
“Malicious actors used typosquatting techniques to deploy custom malicious payloads […] It targets Exodus crypto wallets and uses code injection to leak victims’ credentials to cryptocurrency exchanges,” said Shachar Menashe, Senior Director of JFrog Security Research.
Learn How to Secure Your Identity Perimeter – A Proven Strategy
Improve your business security in our upcoming expert-led cybersecurity webinar: Exploring Identity Perimeter Strategies!
“Our research proves that no open source software repository is completely trustworthy, so we take safeguards at every stage of the software development lifecycle to ensure a secure software supply chain. is needed.”
The findings are based on Phylum’s discovery of a malicious npm package named mathjs-min that was uploaded to the repository on March 26th, 2023 to retrieve Discord passwords from official apps and web browsers such as Google Chrome. This is due to a credential stealer that was found to be lurking. Brave, and opera.
“This package is actually a modified version of the widely used Javascript math library mathjs, which was forked and then injected with malicious code,” said the software supply chain security firm. Said“The modified version was then published to NPM with the intention of passing it off as a minified version of the real mathjs library.”


