SideWinder is a prolific state-of-the-art attacker known to primarily target Pakistan’s military establishments, compromising the official website of the National Electric Power Regulatory Authority (NEPRA), warhawk.
“The newly discovered WarHawk backdoor contains various malicious modules that deliver Cobalt Strike and incorporates new TTPs such as: KernelCallBackTable injection To ensure a winning campaign, we will be checking Pakistan Standard Time Zones.” Zscaler ThreatLabz Said.
The threat group, also known as APT-C-17, Rattlesnake, and Razor Tiger, Suspected However, a Kaspersky report earlier this year acknowledged that previous indicators that led to attribution have since disappeared, making it difficult to tie threat clusters to specific countries.
Over 1,000 attacks are said to have been launched by this group since April 2020. This marks SideWinder’s newfound aggression since its inception ten years ago in 2012.
Intrusions are important not only for their frequency but also their persistence, and the group utilizes a vast arsenal of obfuscated and newly developed components.
In June 2022, it was discovered that the attackers used AntiBot scripts to filter victims and check client browser environments, specifically IP addresses, to confirm that the target was in Pakistan.
The September campaign, spotted by Zscaler, requires the use of weaponized ISO files hosted on NEPRA’s website to activate the kill chain leading to the deployment of WarHawk malware. indicate a justified recommendation Issued by the Cabinet Division of Pakistan on 27th July 2022.
WarHawk spoofs legitimate apps such as ASUS Update Setup and Realtek HD Audio Manager to lure unsuspecting victims into execution, exfiltrates system metadata to hardcoded remote servers, and receives additional payloads from URLs. .
This includes a command execution module responsible for executing system commands on the infected machine received from the C&C server, a file manager module to recursively enumerate files present on various drives, and an upload module to send the files of interest. It is included. to the server.
The Cobalt Strike Loader, which is deployed as a second stage payload using the aforementioned command execution module, also verifies the host’s timezone to ensure it matches Pakistan Standard Time (PKT), and if that fails, the process will Exit.
If all anti-analysis checks pass, the loader injects shellcode into the notepad.exe process using a technique called KernelCallbackTable process injection. technical articles Published in April 2022 by a researcher using the online alias Capt. Meelo.
The shellcode then decrypts and loads the Beacon. Beacon is the default malware payload used by Cobalt Strike to establish connections to command and control servers.
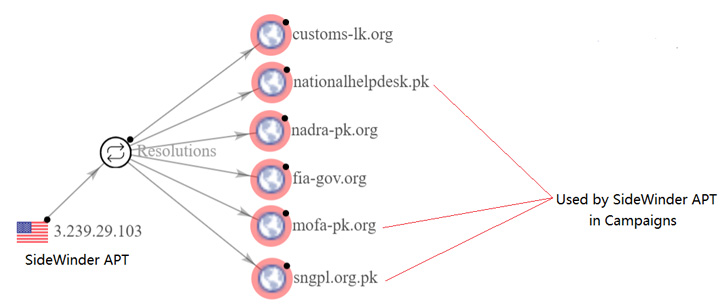
According to the cybersecurity firm, the attack campaign’s connection to the SideWinder APT stemmed from the reuse of network infrastructure identified as being used by the group in previous espionage-focused operations against Pakistan. increase.
“The SideWinder APT group is continuously evolving its tactics and adding new malware to its arsenal to successfully launch targeted espionage campaigns,” concludes the researchers.



