Russia related APT29 The (aka Cozy Bear) threat actor is attributed to ongoing cyber espionage campaigns targeting foreign ministries and agencies located in NATO member states, the European Union, and Africa.
According to Poland’s Military Counterintelligence Service and the CERT Polska team, the observed activity tactically overlaps with a cluster tracked by Microsoft as Nobelium, known for its high-profile attack against SolarWinds in 2020.
The Nobelium operation was carried out by the Russian Foreign Intelligence Service (SVRMore), an organization whose task is to “protect individuals, societies and nations from foreign threats”.
That said, the campaign represents an evolution in the tactics of Kremlin-backed hacking groups, demonstrating continued attempts to improve cyberweapons to penetrate victims’ systems for information gathering. I’m here.
“By using new tools simultaneously, independently of each other, or replacing tools that had become less effective, the attackers were able to maintain a continuous and high operational tempo.” Said.
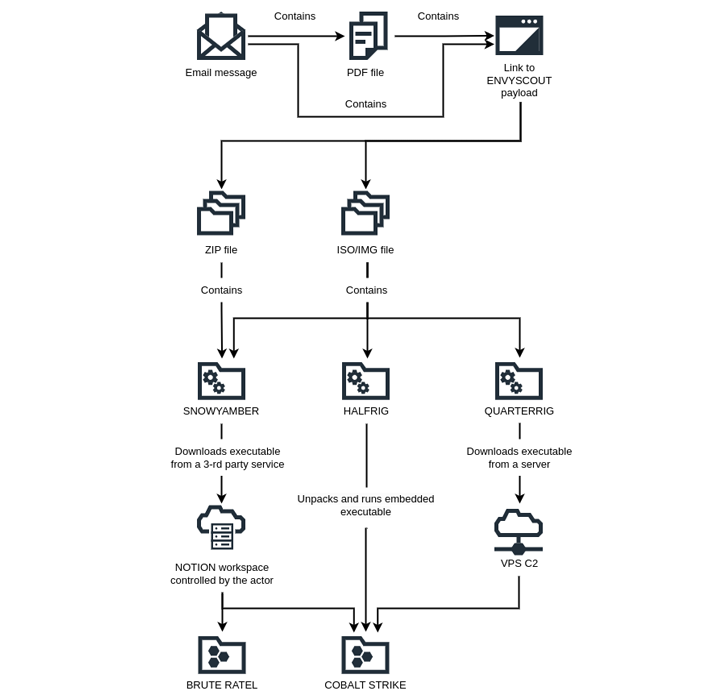
The attack begins with a spear-phishing email impersonating the European Embassy. The email masquerades as an invitation or meeting to trick the targeted diplomat into opening a malware-laden attachment.
A booby-trapped URL embedded within a PDF attachment leads to the deployment of an HTML dropper called EnvyScout (aka ROOTSAW). This dropper is used as a conduit to deliver three previously unknown strains: SNOWYAMBER, HALFRIG, and QUARTERRIG.
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
SNOWYAMBER, also known as GraphicalNeutrino by Recorded Future, utilizes the Notion note taking service for downloading additional payloads such as Command and Control (C2) and Brute Ratel.
QUARTERRIG also acts as a downloader that can retrieve executable files from actor-controlled servers. HALFRIG, on the other hand, acts as a loader that launches the Cobalt Strike post-exploit toolkit contained within.
It’s worth noting that this disclosure is consistent with BlackBerry’s recent findings. BlackBerry details its Nobelium campaign for European Union countries, with a particular focus on institutions “helping Ukrainian citizens fleeing the country and providing assistance to the Ukrainian government.”


