Amazon Web Services (AWS) has resolved a cross-tenant vulnerability in its platform that could be weaponized by an attacker to gain unauthorized access to resources.
This problem, confusing sub-problema type of privilege escalation in which a program without permission to perform an action can force a more privileged entity to perform an action.
This flaw was reported to AWS by Datadog on September 1, 2022, and a patch was subsequently shipped on September 6.
“This attack exploited the AppSync service to [identity and access management] role This allows attackers to infiltrate a victim’s organization and access resources on those accounts,” said Datadog researcher Nick Frichette. Said In a report released last week.
Under joint disclosure, Amazon Said No customers are affected by this vulnerability and no customer action is required.
It states, “A case-sensitive parsing issue within AWS AppSync that could be used to bypass the service’s cross-account role usage validation and perform actions as a service across customer accounts. ‘ explains.
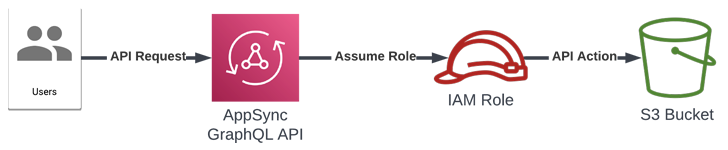
AWS AppSync offer Developers can use GraphQL APIs to retrieve or modify data from multiple data sources and automatically synchronize data between mobile and web applications and the cloud.
The service can also be used to integrate with other AWS services through specific roles designed to make the required API calls with the required IAM permissions.
AWS has a safeguard in place to prevent AppSync from assuming arbitrary roles by validating the role’s Amazon Resource Name (ARN), but this issue is “service roll” parameters are in lower case.
This behavior can be abused to provide an identifier for a role in another AWS account.
“This vulnerability in AWS AppSync allowed an attacker to cross account boundaries and execute AWS API calls on a victim’s account via an IAM role that trusts the AppSync service,” said Frichette. I’m here.
“By using this method, an attacker could compromise an organization using AppSync and gain access to resources associated with those roles.”



