Businesses operating in the Latin America (LATAM) region are being targeted by a new Windows-based banking Trojan called . Totoin Temple After May 2023.
“This sophisticated campaign uses a Trojan horse that follows a multi-stage infection chain with specially crafted modules at each stage,” said Zscaler researchers Niraj Shivtarkar and Preet Kamal. says Mr. Said In a report released last week.
“These modules can be used for malicious purposes such as injecting malicious code into remote processes, bypassing User Account Control with COM elevation monikers, and evading detection by sandboxes through clever techniques such as system reboots and parent process checks. It is custom designed to perform certain activities.”
This six-step approach has all the hallmarks of a well-crafted suite of attacks. First, a phishing email is sent containing an embedded link pointing to a ZIP archive hosted on an Amazon EC2 instance to evade domain-based detection.
This email message uses an invoice-themed decoy to trick unsuspecting recipients into opening it and causing an infection. Inside the ZIP archive is a downloader execution designed to set persistence using LNK files in the Windows Startup folder and communicate with a remote server to retrieve six next-stage payloads in the form of MP3 files. It contains possible files.
The downloader is also responsible for generating a batch script that reboots the system after a 10 second timeout. The researchers say this is done to “avoid sandbox detection, as malicious actions only occur after a reboot.”
The fetched payload contains a valid binary ‘icepdfeditor.exe’ signed by ZOHO Corporation Private Limited which, when executed, launches a malicious DLL (‘ffmpeg.dll’) codenamed Krita Loader. is sideloaded.
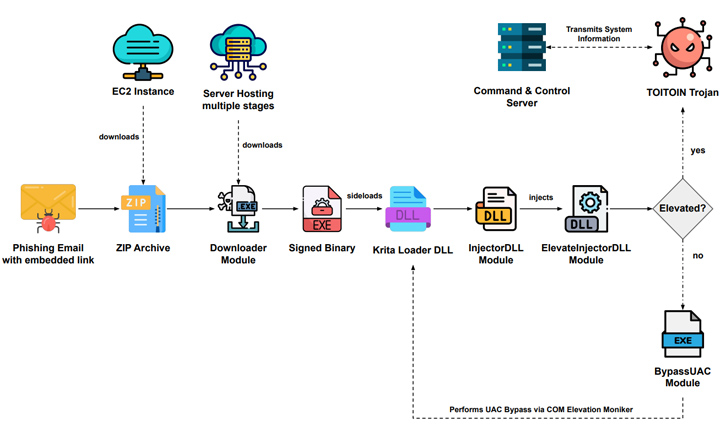
The loader side decodes the JPG file downloaded with the rest of the payload, launches another executable known as the InjectorDLL module, and inverts the second JPG file to form what is called the ElevateInjectorDLL module. is designed to
The InjectorDLL component was then moved to inject ElevateInjectorDLL into the ‘explorer.exe’ process and then User Account Control (UAC) bypasses if necessary, escalates process privileges, decrypts and injects the TOITOIN Trojan into the ‘svchost.exe’ process.
🔐 PAM Security – Expert Solutions to Secure Sensitive Accounts
Gain the knowledge and strategies you need to transform your privileged access security strategy in this expert-led webinar.
“This technique allows malware to manipulate system files and execute commands with elevated privileges, facilitating further malicious activity,” the researchers explained.
TOITOIN has the ability to collect system information as well as data from installed web browsers such as Google Chrome, Microsoft Edge, Internet Explorer, Mozilla Firefox and Opera. Additionally, it checks for the presence of Topaz Online Fraud Detection (OFD). Anti-cheat module Integrated with banking platforms in the Latin America region.
The nature of the response from the command and control (C2) server is currently unknown as the command and control (C2) server is no longer available.
“Through deceptive phishing emails, complex redirection mechanisms, and domain diversification, attackers successfully deliver malicious payloads,” the researchers said. “The multi-stage infection chain observed in this campaign includes the use of custom-developed modules employing various evasion techniques and encryption methods.”


