Publicly traded companies in Vietnam have been targeted as part of an ongoing campaign to deploy a new backdoor called “. Spectra Viper.
“SPECTRALVIPER is a highly obfuscated and previously undisclosed x64 backdoor that provides PE loading and injection, file upload and download, file and directory manipulation, and token impersonation capabilities,” Elastic Security Labs said. Said in Friday’s report.
The attack is believed to be by the actor tracked as REF2754 and overlaps with Vietnamese threat groups known as APT32, Canvas Cyclone (formerly Bismuth), Cobalt Kitty, and OceanLotus.
In December 2020, Meta linked the hacking group’s activities to a cybersecurity firm called CyberOne Group.
The latest infection flow discovered by Elastic is SysInternals procedure dump This utility is used to load unsigned DLL files containing DONUTULOADER. This file is configured to load SPECTRALVIPER and other malware such as P8LOADER and POWERSEAL.
SPECTRALVIPER is designed to connect to an attacker-controlled server and wait for further commands while employing obfuscation techniques such as: Flattening control flow To resist analysis.
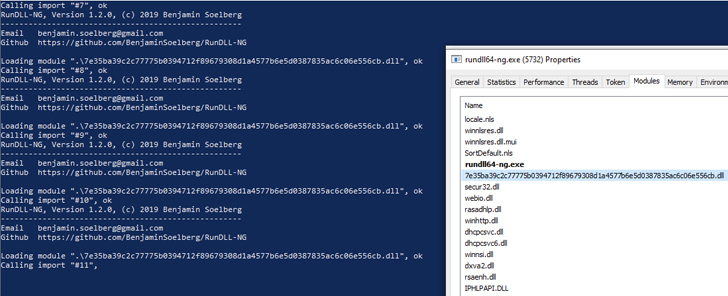
Written in C++, P8LOADER can launch arbitrary payloads from files or memory. It also uses a dedicated PowerShell runner named POWERSEAL that is instrumented to run the provided PowerShell scripts or commands.
REF2754 is said to have tactical similarities with another group REF4322It is known to deploy “post-exploit implants”, primarily targeting companies in Vietnam. Foreal (aka Rizzo).
This link raises the possibility that “both REF4322 and REF2754 activity groups represent campaigns planned and carried out by Vietnam state-related threats.”
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join us for an insightful webinar!
This finding suggests that an intrusion set called REF2924 Somni Records It uses DNS queries to communicate with remote servers and bypass network security controls.
SOMNIRECORD, like NAPLISTENER, leverages existing open source projects and refines its functionality to retrieve information about infected machines, list all running processes, deploy web shells, and extract files already present in the system. Allows launching of executable files.
“The use of open source projects by attackers indicates that attackers are taking steps to customize existing tools for their specific needs, and may be trying to counter attribution attempts. Yes,” the company said.



