Service Location Protocol (SLP) can be weaponized to launch mass denial of service attacks against targets.
Bitsight and Curesec researcher Pedro Umbelino said, “An attacker exploiting this vulnerability could leverage vulnerable instances to launch a massive denial of service (DoS) amplification attack with a multiplier of up to 2200x. This could be one of the largest amplification attacks ever reported.”and Marco Lux Said In a report shared with The Hacker News.
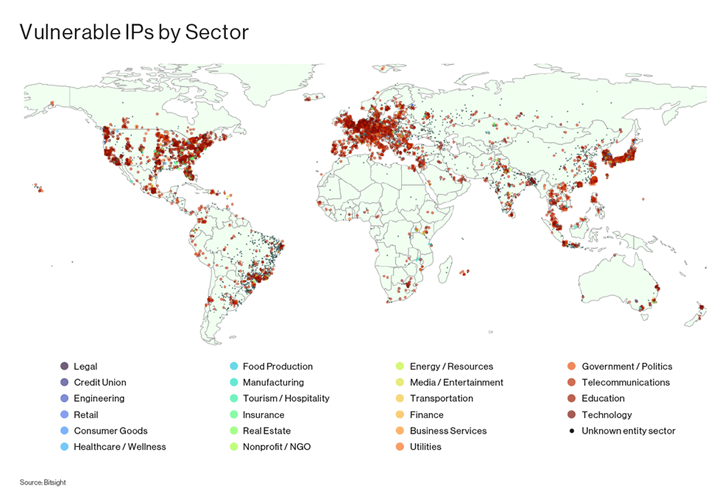
Vulnerabilities with assigned identifiers CVE-2023-29552 (CVSS score: 8.6) is said to affect over 2,000 global organizations and over 54,000 SLP instances accessible over the internet.
This includes VMWare ESXi hypervisors, Konica Minolta printers, Planex routers, IBM Integrated Management Modules (IMMs), SMC IPMI, and 665 other products.
The top 10 countries with the most organizations with vulnerable SLP instances are the United States, United Kingdom, Japan, Germany, Canada, France, Italy, Brazil, the Netherlands, and Spain.
SLP is a service discovery protocol that allows computers and other devices to find services within a local area network, such as printers, file servers, and other network resources.
Successful exploitation of CVE-2023-29552 allows attackers to leverage susceptible SLP instances to reflection amplification attack Overwhelm the targeted server with fake traffic.
To do this, all an attacker would need to do is find an SLP server on UDP port 427 and register a “service until SLP denies further entries”. request spoofing Send to that service using the victim’s IP as the source address.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
This kind of attack can generate an amplification factor of up to 2,200x and cause a massive DoS attack. To mitigate this threat, we recommend disabling SLP on Internet-facing systems or filtering traffic on UDP and TCP port 427 instead.
“It is equally important to enforce strong authentication and access controls, ensure that only authorized users have access to the correct network resources, and closely monitor and audit access,” said the researchers.
Web security company Cloudflare, Recommendationsaid they “expect the prevalence of SLP-based DDoS attacks to increase significantly in the coming weeks,” as attackers experiment with new DDoS amplification vectors.
The findings are due to a two-year-old patched vulnerability in VMware’s SLP implementation that was exploited earlier this year in a widespread attack by actors associated with the ESXiArgs ransomware.


