A little-known Russian-speaking cyber espionage group has been revealed to be involved in a new politically motivated surveillance campaign targeting government officials, telecommunications services and public service infrastructure in Tajikistan. rice field.
intrusion set, dubbed paper bug The attack by Swiss cybersecurity firm PRODAFT nomadic octopus (aka Dust Squad).
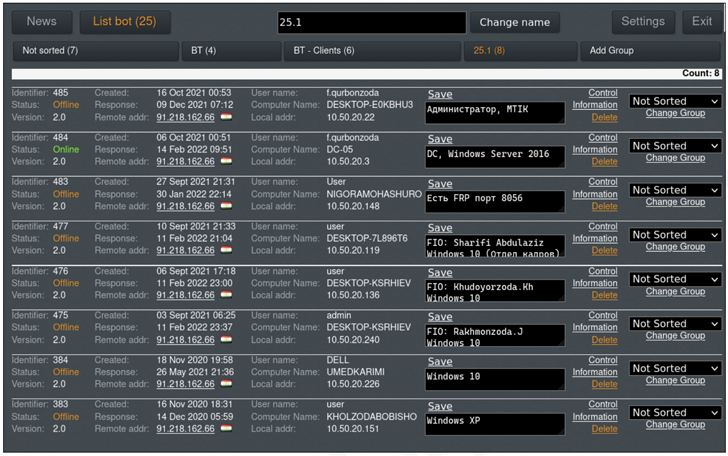
“The types of machines compromised ranged from personal computers to [operational technology] In a detailed technical report shared with The Hacker News, PRODAFT said:
The ultimate motive behind the attack is unknown at this stage, but the cybersecurity firm has raised the possibility that it was the work of domestic opposition forces or an intelligence gathering mission by Russia or China. I’m here.
The Nomadic Octopus first appeared in October 2018. ESET and Kaspersky It details a series of phishing attacks carried out by attackers against several Central Asian countries. The group is believed to have been active since at least 2014.
Cyberattacks have included using custom Android and Windows malware to attack high-value organizations such as local governments, diplomatic missions, and political bloggers, and suggesting that attackers are involved in cybersurveillance activities. are more likely to be.
Windows malware called octopus Also a Delphi-based tool masquerading as an alternate version of the Telegram messaging app that allows the attacker to monitor victims, siphon sensitive data, and gain backdoor access to the system via a command and control (C2) panel. allows you to
Subsequent analysis by Gcow security December 2019 saw a notable attack by an Advanced Persistent Threat (APT) group against the Uzbekistan Ministry of Foreign Affairs aimed at deploying Octopus.
PRODAFT’s findings are the result of the discovery of an operational environment managed by Nomadic Octopus since 2020, making Paperbug the first campaign orchestrated by the group since Octopus.
Data collected by the company shows that after successfully gaining access to a telecom company’s network, the threat actor spread laterally to more than 10 targets focused on government networks, executives, and OT devices with known vulnerabilities. moved. It is not known exactly when and how the communication network was compromised.
“Operation PaperBug is consistent with a general trend of attacks on Central Asian government infrastructure that has become more pronounced in recent times,” PRODAFT said.
Nomadic Octopus is believed to exhibit some level of affiliation with another Russian state actor known as Sofacy (aka APT28, Fancy Bear, Forest Blizzard, or FROZENLAKE). victimology overlap.
The latest attacks also used Octopus variants with the ability to take screenshots, execute commands remotely, download and upload files to and from infected hosts to remote servers. .something like that artifact Uploaded to VirusTotal on April 1, 2021.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
A closer look at the command and control (C2) servers revealed that the group had successfully backdoored a total of 499 systems as of January 27, 2022. Among them were government network devices, gas stations, and cash registers.
However, the group does not appear to possess an advanced toolset, and despite the high risk of the attack, does not appear to be very interested in hiding traces of the victim’s machine.
“When operating on a compromised machine to steal information, we sometimes inadvertently displayed permission pop-ups on the victim’s computer, resulting in arousal of suspicion by the victim,” the company said. pointed out. “However, this was resolved as the group diligently named the files they transferred as harmless and unobtrusive programs.”
The same tactic extends to naming their malicious tools. The group camouflages themselves as popular web browsers such as Google Chrome, Mozilla Firefox, and Yandex to keep a low profile.
That said, Paperbug’s attack chain is largely characterized by the use of common attack tools and common techniques, effectively acting as a “hide” for the group and making attribution more difficult. .
“This imbalance between operator skill and mission importance may indicate that the operator was recruited by some entity that provided a list of commands that had to be executed precisely on each machine. There is,” PRODAFT said, adding, “Operators are forced to create a checklist and stick to it.”


