New ATM malware stock dubbed fix has been observed targeting Mexican banks since early February 2023.
“ATM malware is hidden inside another seemingly harmless program,” says Latin American cybersecurity firm Metabase Q. Said In a report shared with The Hacker News.
Windows-based ATM malware not only requires interaction via an external keyboard, but is vendor agnostic and capable of infecting any teller machine it supports. CEN/XFS (short for eXtensions for Financial Services).
The exact method of intrusion remains unknown, but Metabase Q’s Dan Regalado told The Hacker News that it’s likely that “the attacker found a way to interact with the ATM via the touchscreen.” .
FiXS is also said to resemble another strain. ATM malware Code name Plutus This allowed cybercriminals to use external keyboards or withdraw cash from ATMs. Sending SMS messages.
One of the notable features of FixS is that 30 minutes after the ATM’s last reboot, Windows GetTickCount API.
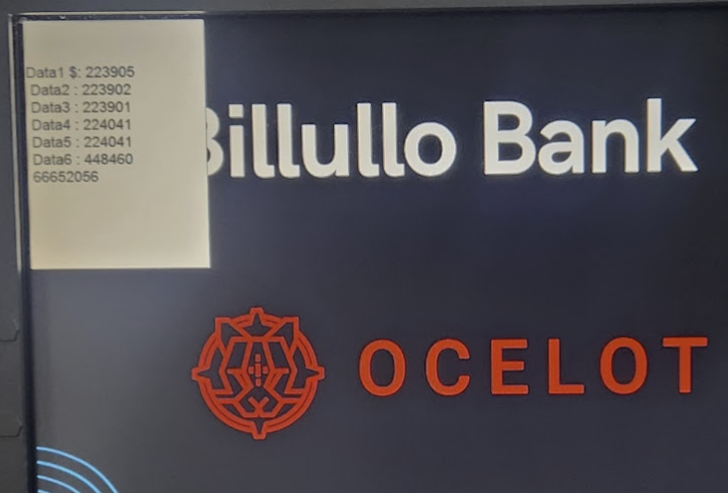
of sample Data analyzed by Metabase Q dropper known as Nesta (conhost.exe), file infection virus It is coded in Delphi and was first seen in 2003.
“FiXS is implemented with the CEN XFS API and can run on almost any Windows-based ATM with very little adjustment. ripper“The way FixS interacts with criminals is through an external keyboard.”
With this development, FixS is the latest in a long list of malware such as: PlutusPrex, Successful, green dispenserRipper, Alice, ATMitch, Skimmerand ATMii Targeting ATMs to siphon money.
Discover the latest malware evasion tactics and defense strategies
Ready to demystify the 9 most dangerous misconceptions about file-based attacks? Join our upcoming webinar and become a hero in the fight against patient zero infections and zero-day security events!
Pilex then evolved into a modular point-of-sale (PoS) malware that carried out credit card fraud in a variety of ways, including blocking contactless payment transactions.
“Cybercriminals who compromise networks have the same end goal as those who carry out attacks through physical access: distributing cash.” Trend Micro Said A detailed report on ATM malware published in September 2017.
“But instead of manually installing malware into an ATM via USB or CD, criminals don’t have to go to the machine anymore. They have a standby money mule to pick up the cash and run away.”


