Entities located in East Asia, Southeast Asia, and Ukraine have been targeted by a subgroup of APT41, a previously undocumented Chinese Advanced Persistent Threat (APT) since at least 2020.
Cybersecurity company Trend Micro baptized agent earth longyisaid the attacker’s long-running campaign can be split into two based on the toolset deployed to attack the victim.
The first wave, from May 2020 to February 2021, is said to have targeted Taiwan’s government, infrastructure, healthcare industry, and China’s banking sector. some countries in Asia.
This includes defense, aviation, insurance and urban development industries in Taiwan, China, Thailand, Malaysia, Indonesia, Pakistan and Ukraine.
The victim pattern and targeted sectors overlap with attacks launched by Earth Baku, a sister group of APT41 (aka Winnti), the Japanese cybersecurity firm added.
Some of Earth Baku’s malicious cyber activities are associated with groups that other cybersecurity companies ESET and Symantec refer to as SparklingGoblin and Grayfly, respectively.
“SparklingGoblin’s Tactics, Techniques, and Procedures (TTPs) partially overlap with APT41’s TTPs,” ESET researcher Mathieu Tartare previously told The Hacker News. “Symantec’s definition of Greyfly appears to overlap (at least partially) with SparklingGoblin.”
Now Earth Longzhi is adding another piece of the APT41 attack puzzle, and the actors also share a link to the dubbed third subgroup. Group CC (aka APT17, Aurora Panda, or Bronze Keystone).
Attacks orchestrated by hacker groups use spear phishing emails as the initial entry point. These messages are known to embed links to files hosted in password-protected archives or Google Drive. Opening these launches a Cobalt Strike loader called CroxLoader.
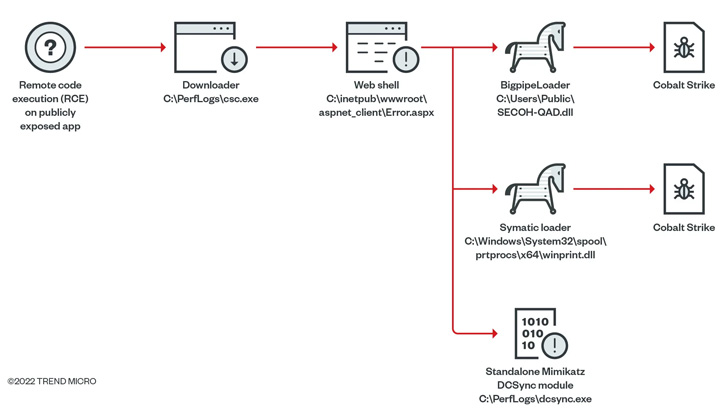
In some cases, the group has weaponized remote code execution flaws in published applications, providing a web shell that can drop a next-stage loader called Symatic designed to deploy Cobalt Strike. is observed.
Also used as part of post-exploitation activity is an “all-in-one tool” that combines public and custom functionality into a single package, believed to have been available since September 2014. increase.
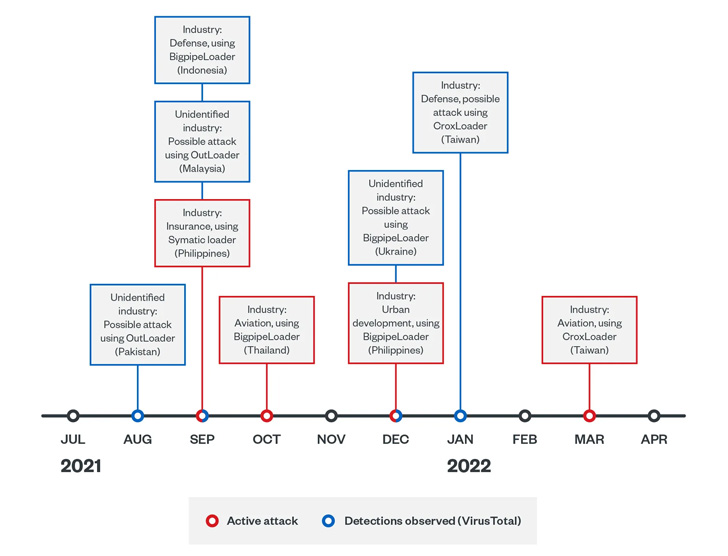
A second series of attacks launched by Earth Longzhi follows a similar pattern. The main difference is that Red Team drops his framework on infected hosts using different Cobalt Strike loaders named CroxLoader, BigpipeLoader, and OutLoader.
Recent attacks have used custom tools that can disable security software, use modified versions of Mimikatz to dump credentials, and exploit flaws in Windows print spooler components (such as PrintNightmare) to escalate privileges. Use is even more pronounced.
Additionally, the neutralization of installed security solutions is performed by a method known as Bring Your Own Vulnerable Driver (BYOVD). This involves exploiting a known flaw in the RTCore64.sys driver (CVE-2019-16098).
This is done using ProcBurner, a tool for killing specific running processes, but another custom malware called AVBurner is used to kill the process by removing the process creation callback. Deregister the point detection and response (EDR) system. detailed By a security researcher who goes by the alias brsn in August 2020.
Please note that in recent months, multiple threat actors such as BlackByte and OldGremlin have used outdated versions of the RTCore64.sys driver that still have valid digital signatures.
“[Earth Longzhi’s] The targeted sectors are those related to national security and economics in Asia-Pacific countries,” said the researchers.
“The group uses social engineering techniques to spread malware and deploy customized hacking tools to evade the protection of security products and steal sensitive data from compromised machines.”



