Iran related muddy water The attackers have been observed targeting several countries in the Middle East, Central and West Asia as part of a new spear-phishing campaign.
“This campaign has been confirmed to target Armenia, Azerbaijan, Egypt, Iraq, Israel, Jordan, Oman, Qatar, Tajikistan and the United Arab Emirates,” said Deep Instinct researcher Simon Kenin. increase. Said in technical articles.
MuddyWater, also known as Boggy Serpens, Cobalt Ulster, Earth Vetala, Mercury, Seedworm, Static Kitten, TEMP.Zagros, is said to be a sub-element within Iran’s Ministry of Information Security (MOIS).
Active since at least 2017, attacks launched by this spy group typically target the telecommunications, government, defense, and oil sectors.
The current intrusion set follows MuddyWater’s long-standing tactic using phishing lures containing document attachments embedded with direct links to Dropbox or URLs pointing to ZIP archive files.
Note that the message was sent from a corporate email account that has already been compromised. put up for sale Darknet by webmail shops such as Xleet, Odin, Xmina, Lufix, etc. range from $8 to $25 per account.
The archive file previously contained installers for legitimate tools such as ScreenConnect and RemoteUtilities, but the attackers were observed to discreetly switch to Atera Agent in July 2022.
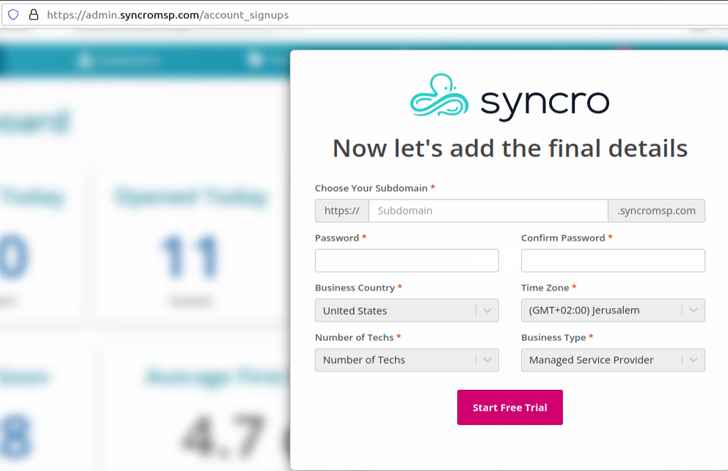
However, in a further sign that the campaign is being actively maintained and updated, the attack tactics have been tweaked again and offered another remote management tool called Syncro.
of Integrated MSP software It offers a way to take full control of the machine, allowing adversaries to conduct reconnaissance, deploy additional backdoors, and even sell access to other actors.
“An attacker who gains access to corporate machines through such functionality has almost limitless options,” said Kenin.
The findings are also newly discovered by Deep Instinct. Malware component Hired by a Lebanese-based group and tracked as Polonium in attacks aimed solely at Israeli organizations.
“Polonium is coordinating its operations with multiple tracked adversary groups affiliated with Iran’s Ministry of Information and Security (MOIS) based on victim overlap and the following common techniques and tools.” Microsoft pointed out in June 2022.



