Google has removed two new malicious dropper apps from the Android Play Store. One of them was disguised as a lifestyle app distributing Xenomorph banking malware.
“Xenomorph is a Trojan that steals credentials from banking applications on users’ devices,” said Zscaler ThreatLabz researchers Himanshu Sharma and Viral Gandhi. Said In an analysis released Thursday.
“It can also intercept users’ SMS messages and notifications, allowing them to steal one-time passwords and multi-factor authentication requests.”
The cybersecurity firm said it also found an expense tracking app exhibiting similar behavior, but said it was unable to extract the URL used to retrieve the malware artifacts.
The two malicious apps are:
- Todo: Day Manager (com.todo.daymanager)
- Expense Keeper (com.setprice.expenses)
Both apps work as droppers. So the app itself is harmless, and in Todo’s case he’s a pipe to get the actual payload hosted on GitHub.
First documented by ThreatFabric in February of this year, Xenomorph is known for abusing Android’s accessibility permissions to conduct overlay attacks. In this attack, a fake login screen is displayed over a legitimate banking app to steal the victim’s credentials.
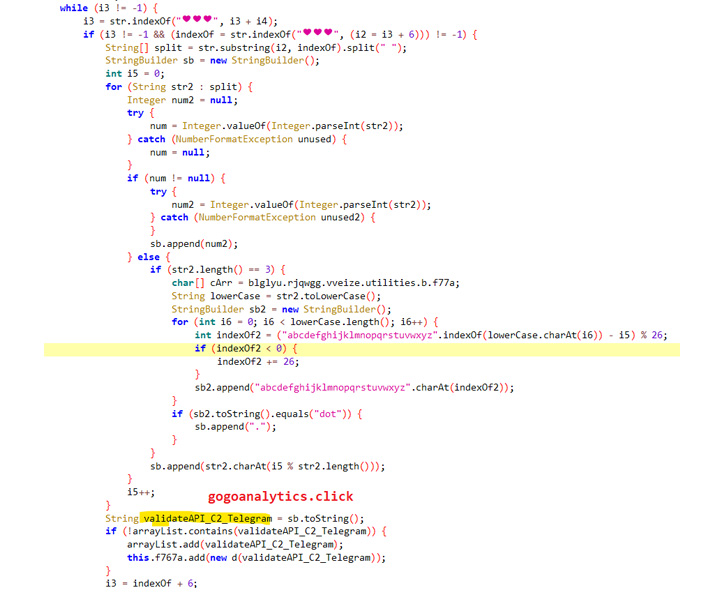
Additionally, the malware leverages the Telegram channel description to decode and construct a command and control (C2) domain used to receive additional commands.
This development follows the discovery of four malicious apps on Google Play that were found to direct victims to malicious websites as part of an adware and information theft campaign. Google told The Hacker News that it has since banned the developer.



