of dark pink Advanced Persistent Threat (APT) actors have been linked to a new series of attacks targeting government and military entities in Southeast Asian countries using malware called KamiKakaBot.
Dark Pink, also known as Saaiwc, was first profiled by Group-IB earlier this year and said it used custom tools like TelePowerBot and KamiKakaBot to execute arbitrary commands and steal sensitive information.
The threat actor is suspected to originate from the Asia-Pacific region and has been active since at least mid-2021, with an increase in tempo observed in 2022.
“The latest attack, which occurred in February 2023, was almost identical to the previous one,” says Dutch cybersecurity firm EclecticIQ disclosed In a new report released last week.
“The main difference in the February campaign was that the malware obfuscation routines were improved, making it easier to evade antimalware.”
The attack takes the form of a social engineering lure that delivers the malware by attaching an ISO image file to an email message.
The ISO image contains an executable (Winword.exe), a loader (MSVCR100.dll) and a decoy Microsoft Word document, the latter of which contains the KamiKakaBot payload.
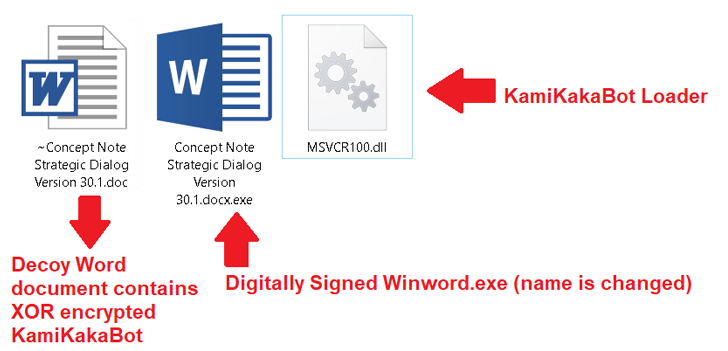
The loader, as part of it, is designed to load the KamiKakaBot malware. DLL sideloading method Bypasses security protections and loads the Winword.exe binary into memory.
KamiKakaBot is primarily designed to steal data stored in web browsers and execute remote code using Command Prompt (cmd.exe). It also employs evasive techniques that blend into the victim’s environment and hinder detection.
Discover the hidden dangers of third-party SaaS apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions granted and how to minimize the risks.
Persistence on a compromised host is Winlogon helper library Make malicious Windows registry key changes. The collected data is then exfiltrated to the Telegram bot as a ZIP archive.
“Using legitimate web services such as Telegram as command and control (C2) servers remains the first choice for a wide range of threat actors, from routine cybercriminals to advanced and persistent threat actors,” he said. , said the Amsterdam-based company.
“During its February 2023 campaign, the Dark Pink APT group is very likely a threat actor motivated by cyber espionage, specifically exploiting ties between ASEAN and European countries to create phishing lures. It is high.”


