A new malware campaign has been observed using sensitive information stolen from banks as lures in phishing emails to drop remote access Trojans. BitRAT.
An unknown attacker allegedly hijacked the IT infrastructure of a Colombian cooperative bank and used the information to craft a convincing decoy message to lure victims into opening a suspicious Excel attachment. It is
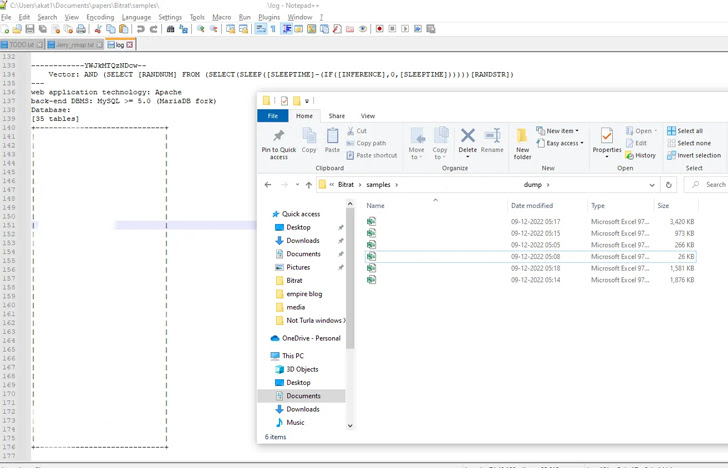
The discovery comes from Qualys, a cybersecurity company. found Evidence of a database dump consisting of 418,777 records allegedly obtained by exploiting a SQL injection fault.
The leaked details included Cédula numbers (national ID documents issued to Colombian citizens), email addresses, phone numbers, customer names, payment records, salary details, addresses, and more.
There is no evidence that the information was previously shared on darknet or clear web forums, suggesting that the attackers themselves accessed customer data to launch phishing attacks.
The Excel file containing the exfiltrated banking data also embeds a macro used to download a second stage DLL payload configured to retrieve and execute BitRAT on the compromised host.
Qualys researcher Akshat Pradhan said, “We use the WinHTTP library to download the BitRAT embedded payload from GitHub to the %temp% directory.
A GitHub repository created in mid-November 2022 is used to host an obfuscated BitRAT loader sample that is eventually decoded and launched to complete the infection chain.
BitRAT, a commercial malware that sells for as little as $20 on underground forums, has extensive capabilities to steal data, gather credentials, mine cryptocurrency, and download additional binaries. increase.
“Commercial off-the-shelf RATs have evolved the way they spread and infect victims,” said Pradhan. “They are also increasing their use of legitimate infrastructure to host their payloads, and defenders should account for that.”


