South Korean and US e-commerce industries are on the receiving end of the ongoing GuLoader malware campaign, cybersecurity firm Trellix revealed late last month.
The malspam campaign is notable for moving from malware-laced Microsoft Word documents to NSIS executables for loading malware. Other countries targeted as part of the campaign include Germany, Saudi Arabia, Taiwan and Japan.
NSISstands for Nullsoft Scriptable Install System, a script-driven open source system used to develop installers for Windows operating systems.
While a series of attacks in 2021 utilized ZIP archives containing macro-laced Word documents to drop executables that loaded GuLoader, a new wave of phishing attempts to embed them in ZIP or ISO images. It uses the downloaded NSIS file to activate the infection.
“By embedding malicious executables in archives and images, attackers may help evade detection,” said Trellix researcher Nico Paulo Yturriaga. Said.
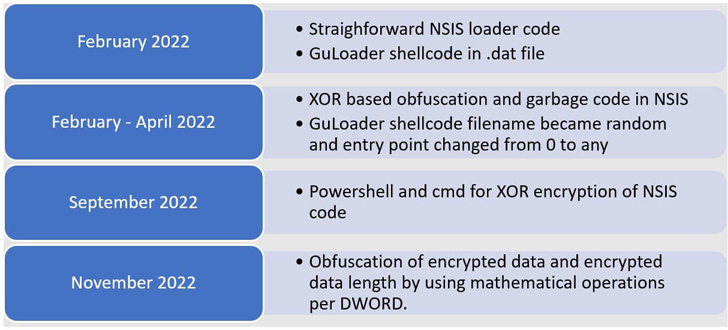
Over the course of 2022, the NSIS scripts used to deliver GuLoader are said to have become more sophisticated, incorporating additional obfuscation and encryption layers to hide the shellcode.
The development also marks a broader shift in the threat landscape, with another method of malware distribution proliferating in response to Microsoft’s blocking of macros in Office files downloaded from the Internet.
“Moving the GuLoader shellcode to an NSIS executable is a remarkable example of the creativity and persistence of attackers in evading detection, preventing sandbox analysis, and thwarting reverse engineering,” said Yturriaga. I’m here.


