A major LastPass breach was caused by one of our engineers failing to update Plex on his home computer, making us realize the dangers of failing to keep software up to date.
The troubled password management service last week revealed how an unidentified attacker used information stolen from previous incidents that occurred prior to August 12, 2022, claiming that it was a “third-party details available from data breaches and vulnerabilities in third-party media software.” A package to launch a second coordinated attack between August and October 2022.”
This intrusion ultimately allowed the attacker to steal partially encrypted password vault data and customer information.
In the second attack, one of the four DevOps engineers was identified to use keylogger malware to target home computers and obtain credentials to compromise cloud storage environments.
This was allegedly made possible by exploiting a now-patched flaw that occurred almost three years ago in Plex to run code on the engineers’ computers.
The vulnerability in question is CVE-2020-5741 (CVSS score: 7.2), a deserialization flaw affecting Plex Media Server on Windows that allows a remote, authenticated attacker to execute arbitrary Python code in the context of the current operating system user .
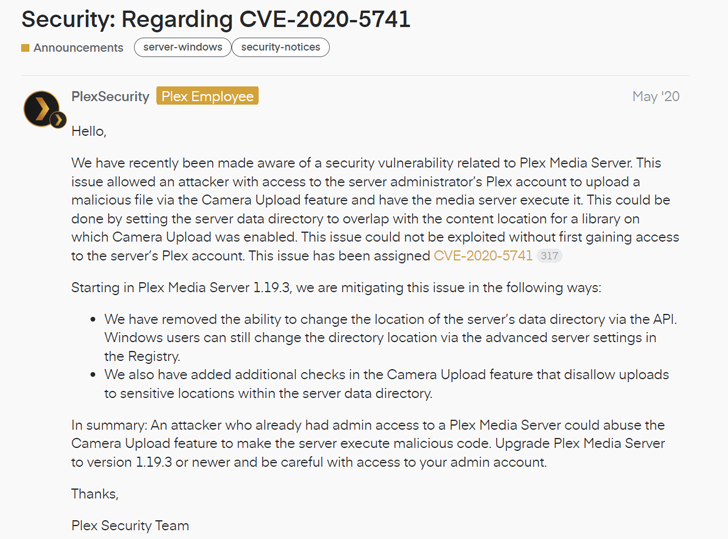
“This issue allowed an attacker with access to a server administrator’s Plex account to upload a malicious file via the camera upload feature and force the media server to execute it,” Plex said. increase. Said In an advisory issued at the time.
Discover the latest malware evasion tactics and defense strategies
Ready to demystify the 9 most dangerous misconceptions about file-based attacks? Join our upcoming webinar and become a hero in the fight against patient zero infections and zero-day security events!
The problem is, discover and report Sent to Plex by Tenable in March 2020 and addressed by Plex in March 2020. Version 1.19.3.2764 Released May 7, 2020. The current version of Plex is 1.31.1.6733.
“Unfortunately, LastPass employees never upgraded their software to enable the patch,” Plex said in a statement. “For reference, the version that addressed this exploit is about 75 versions ago.”


