Advanced Persistent Threat (APT) actors known as dragon breath It has been observed to add a new layer of complexity to attacks by employing novel DLL sideloading mechanism.
“This attack is based on a traditional sideloading attack consisting of a clean application, a malicious loader, and an encrypted payload, with various modifications to these components over time.” Sophos researcher Gabor Szappanos said. Said.
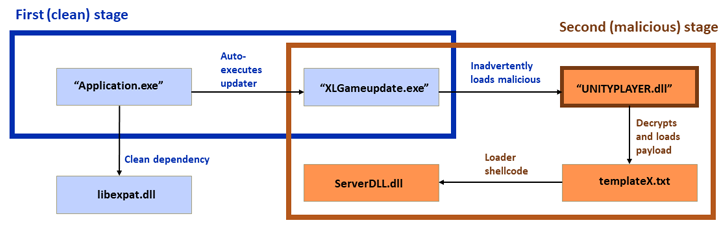
“The latest campaign has a twist where the first stage clean application “sides” loads the second clean application and executes it automatically. A second clean application sideloads a malicious loader DLL. A malicious loader DLL is then executed. final payload. ”
Operation Dragon Breath was also tracked under the names APT-Q-27 and Golden Eye. beginning documented In 2020, QiAnXin detailed a watering hole campaign designed to trick users into downloading a trojanized Windows installer for Telegram.
a successor motion A study detailed by a Chinese cybersecurity firm in May 2022 highlighted the continued use of the Telegram installer as a lure to deploy additional payloads such as the gh0st RAT.
Dragon Breath is also said to be part of a larger organization called the Miuuti Group. The adversary is characterized as a “Chinese-speaking” organization targeting the online gaming and gambling industry, joining other Chinese activity clusters such as Dragon Castling. dragon danceEarth Berberoka.
According to Sophos, the double-dip DLL sideloading strategy has been used in attacks targeting users in the Philippines, Japan, Taiwan, Singapore, Hong Kong, and China. These intrusion attempts were ultimately unsuccessful.
The first vector is a fake website that hosts an installer for Telegram that, when opened, creates a desktop shortcut designed to load a malicious component in the background on startup, while also tricking the victim into opening the Telegram app. display the user interface of
Additionally, the attackers are believed to have created multiple variations of the scheme to start the attack chain using modified installers of other apps such as LetsVPN and WhatsApp.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
The next stage uses a second clean application as an intermediate to evade detection and load the final payload via a malicious DLL.
The payload acts as a backdoor capable of downloading and executing files, clearing event logs, extracting and setting clipboard contents, executing arbitrary commands, and stealing cryptocurrencies from the MetaMask wallet extension for Google Chrome. .
“DLL sideloading, first observed in Windows products in 2010, is widespread across multiple platforms and continues to be an effective and attractive tactic for attackers,” said Szappanos.
“This double-clean app technology employed by the Dragon Breath Group, aimed at a user sector that has hitherto been under-scrutinized by security researchers (online gambling), represents the continued vigor of this approach. .”



