A notoriously advanced and persistent threat actor known as mustang panda is associated with a series of spear-phishing attacks targeting government, education, and research sectors around the world.
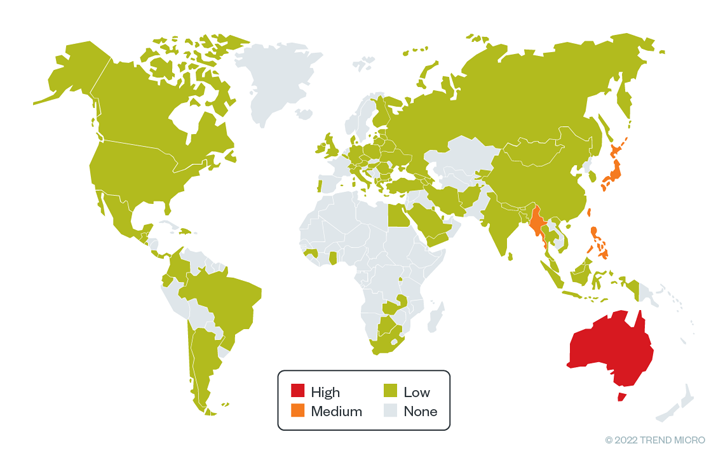
Major targets for incursions from May to October 2022 included counties in the Asia-Pacific region such as Myanmar, Australia, Philippines, Japan, and Taiwan. Said in Friday’s report.
Mustang Panda, also known as Bronze President, Earth Preta, HoneyMyte, and Red Lich, is a China-based spy actor believed to have been active since at least July 2018. Collect data from compromised environments.
The group’s activity, documented by ESET, Google, Proofpoint, Cisco Talos, and Secureworks this year, has seen attackers using PlugX (and its variant called Hodur) to infect various entities in Asia, Europe, and the Middle East. pattern was revealed. , and the Americas.
According to Trend Micro’s latest findings, Mustang Panda continues to evolve its tactics with strategies of evading detection and employing infection routines, leading to the deployment of bespoke malware families such as TONEINS, TONESHELL, and PUBLOAD.
“Earth Preta used fake Google accounts to distribute malware via spear phishing emails, initially stored in archive files (RAR/ZIP/JAR, etc.) and distributed via Google Drive links. ,” said researchers Nick Dai, Vickie Su and Sunny Lu. Said.
Initial access is facilitated by decoy documents covering controversial geopolitical themes, luring targeted organizations to download and trigger malware.
In some cases, phishing messages were sent from previously compromised email accounts belonging to certain entities. This demonstrates the efforts Mustang Panda actors made to increase the chances of a successful campaign.
It is designed to display the lure document to the victim when the archive file is opened. DLL sideloading.
The attack chain ultimately leads to delivery of three malware families: PUBLOAD, TONEINS, and TONESHELL. These can download the next stage payload and fly under the radar.
The primary backdoor used in the attack, TONESHELL, is a shellcode loader installed through TONEINS that uses an early version of the implant that was detected in September 2021, and some of the threat actors have suggests an ongoing effort to update the .
“Earth Preta is a cyber espionage group known for developing its own loader in combination with existing compromise tools such as PlugX and Cobalt Strike,” concludes the researchers.
“Once the group infiltrates a targeted victim’s system, stolen sensitive documents can be exploited as an entry vector for the next wave of intrusions. expand.”


