Introduced as part of code changes dating back to October 2000, a critical vulnerability has been disclosed in the SQLite database library that could allow an attacker to crash or take control of the program.
tracked as CVE-2022-35737 (CVSS score: 7.5), 22 year old issue affects SQLite version 1.0.12 Up to 3.39.1, and has been addressed in Version 3.39.2 Released on July 21, 2022.
“CVE-2022-35737 is Exploitable Exploitability depends on how the program was compiled,” said Trail of Bits researcher Andreas Kellas. Said In a technical article published today.
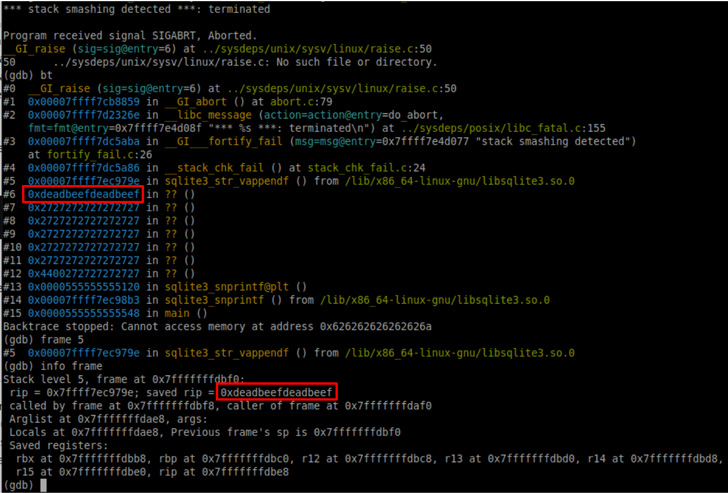
“If the library was compiled without a stack canary, arbitrary code execution is checked, but if a stack canary is present, it is unchecked, and Denial of Service is checked in all cases.”
programmed in C, SQLite that is most widely used database engineAndroid, iOS, Windows, and macOS by default, as well as popular web browsers such as Google Chrome, Mozilla Firefox, and Apple Safari.
The vulnerability discovered by Trail of Bits is integer overflow bug This happens when a very large string input is passed as a parameter to the SQLite implementation. printf functionthen use another function to handle the string formatting (“sqlite3_str_vappendf”).
However, the defective bank is successfully weaponized based on the preconditions contained in the string. Replacement type in the form %Q, %q, or %wIf user-controlled data is written beyond the bounds of a stack-allocated buffer, the program can crash.
“Using special characters to enable scanning of Unicode characters if the format string contains a ‘!’ will in the worst case result in arbitrary code execution or a program hang (almost) It can loop indefinitely,” explains Kellas.
This vulnerability is also an example of a scenario that would have been considered impractical decades ago: assigning a 1GB string as input. 64-bit computing system.
“This is a bug that might not have looked like an error when it was written (SQLite source code dates back to 2000) when the system was primarily a 32-bit architecture,” Kellas said. I’m here.



