Neither cryptocurrencies nor ransomware are new to the digital world. Both have been there for a very long time, enough to find common ground to start a relationship.
Ransomware can be like a virtual car that runs on all sorts of fuels, with cryptocurrencies being the most preferred today. No one claims that 2020 was the year of ransomware in the cyber world, but not because of the fact that cybercriminals chose ransomware simply because they know how to attack it properly. This is because cryptocurrencies have risen significantly this year along with the new normal of the digital world. The ability to pay anonymously using cryptocurrencies has given them another reason to stick with ransomware.
How does ransomware work?
Ransomware is a type of malware that encrypts the victim’s files, denying access to files on personal devices, whether it’s a random user or an organization.
The key to gaining access is to pay the attacker a ransom.
How are cryptocurrencies helping spread ransomware?
Now we know that all crypto transactions are untraceable for both receiver and sender. This is called the entire anonymous transaction. The increased demand for crypto in recent years has made it easier to buy and sell these virtual coins and win real money.
That said, cryptocurrency has become the preferred (if not the best) way for cybercriminals to get ransom money without tracking and grant those organizations access to their files. rice field.
How to avoid joining a ransomware party?
Most of the articles on the Internet provide instructions on how to minimize losses and make no mistakes and pass the ransom money to the criminals to ensure your files back. But the question is, why should we learn how to pay criminals when we can avoid encountering them and their viruses in the first place?
There are multiple methods, each offering a generous percentage of protection.
Start by taking a cybersecurity awareness training course called Ultimate Layers of Protection, then layer up, such as the first and most valuable layer that works at the DNS level. The DNS level is the first gate between users and cybercriminals.
Strong DNS protection just turns the wheel every time you try to run a website that contains viruses. It also blocks all cryptocurrency and mining websites that most hackers participate in.
Do you have an example?
absolutely.
Dark Side Ransomware. Its active activity took place in 2020. Its main feature was to encrypt the victim’s data as well as delete it from the affected servers. This is one of the characteristics of such threats.
In less than a year of work, about $100 million has been paid out in Bitcoin. The blackmailer received about $10 million just for attacking two companies.
Brenntag sells chemicals. In this case, her DarkSide partner involved in the crime said she gained access to the network after purchasing the stolen information, but didn’t know how she got the credentials in the first place. The company is cryptocurrency and he paid a ransom of $4.4 million. Following the ransom payment, Brentag obtained a decryption tool for encrypted files and successfully stopped cybercriminals from exposing the company’s stolen information.
The second company is Colonial Pipeline. The Colonial Pipeline is the largest refined petroleum products pipeline system in the United States. After being found to be a “victim of a cybersecurity attack,” the pipeline operator took some systems offline, temporarily suspending pipeline operations and several IT systems. We also contacted an outside cybersecurity firm to conduct an investigation. Finally, they paid the hackers around $5 million in cryptocurrency in exchange for a decryption key to restore their system.
Conti ransomware. The main victims of this extortion were medical institutions. Its usual method is to use phishing attacks to gain remote access to computers and spread further over the network, while stealing credentials and gathering unencrypted data. And the most famous attack was against an Irish health service executive. In this attack, the gang demanded a ransom of approximately $20 million in cryptocurrency to keep the data they received private.
to get protection?
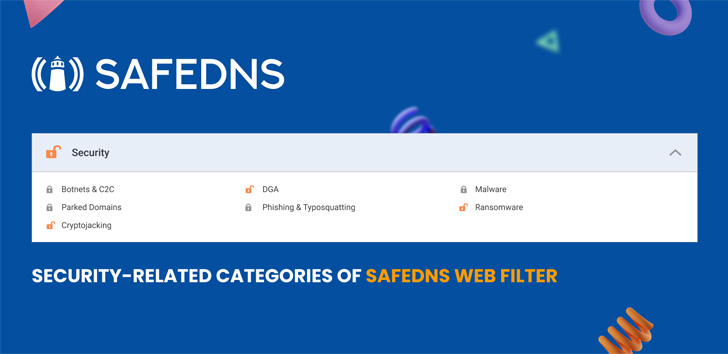
SafeDNS updated categories to include DGA, cryptojacking, etc. as part of their security groups. 15 days free trial Try web filtering. Take care!


